Hello peeps 🐥
This article is all about utilizing my lock-down time in finding bugs under a private program whose name has to be redacted here. █████’s program is active since years with list of professional & responsible hackers named in their **Hall Of Fame **till today’s year. Still I managed to find multiple XSS and escalated impact of one XSS to sensitive data stealing. So let’s get started 🤙.
Note: This article wants to help new-comers to understand impact escalation and get in-depth knowledge for XSS vulnerabilities.
Timeline:
14.04.2020
Turned on machine, started active + passive discovery of domains and all in-scope assets of █████. Used many tools like _Sublist3r, Amass, findomain, subfinder, etc. _At last I merged all outputs and made one list.
I believe less in automation testing and laziness 🙃 so I sorted the list and probed them all. Visited each domain one-by-one and ffufed domains which seemed potentially juicy to me. This game goes on.
17.04.2020
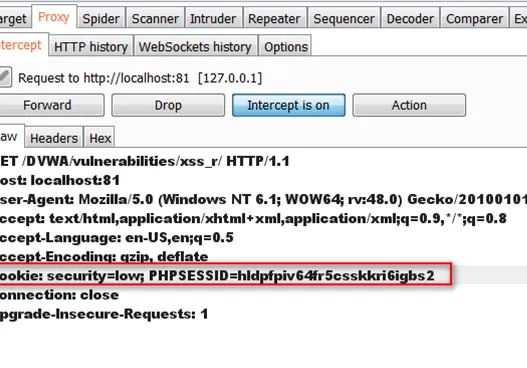
After 2 days of manually doing everything, for a domain I got a good list of endpoints using waybackurls, used Arjun to find valid parameters and then got a beautiful reflection 😍.
#bug-bounty #pentesting #bug-hunting #infosec #data visualization