This tutorial will show you how to set up SSH two-factor authentication on Ubuntu server using the well-known Google Authenticator. It will greatly improve the security of the SSH service on your Ubuntu server.
How Two-Factor Authentication Works
Normally, you only need to enter a password or use SSH key to log in to your Ubuntu server remotely. Two-factor authentication (2FA) requires you to enter two pieces of information in order to login. So you will also need to enter a time-based one-time password to log in to your SSH server. This one-time password is computed using the TOTP algorithm, which is an IETF standard. These days many websites and services (Facebook, Google, Twitter, etc) offer 2FA for users to secure their accounts and it’s a good idea to also enable 2FA on your SSH server.
This tutorial will show you how to set up
- Password authentication with a one-time password
- Public key authentication with a one-time password
Note: The open-source server software we will use in this article is called libpam-google-authenticator, which is installed from the default Ubuntu repository. Google the company does not involve in the authentication process in any shape or form. The server software and the mobile app don’t need network access.Step 1: Install and Configure Google Authenticator on Ubuntu Server
Log into your Ubuntu server and run the following command to install Google Authenticator from the default Ubuntu package repository.
sudo apt install libpam-google-authenticator
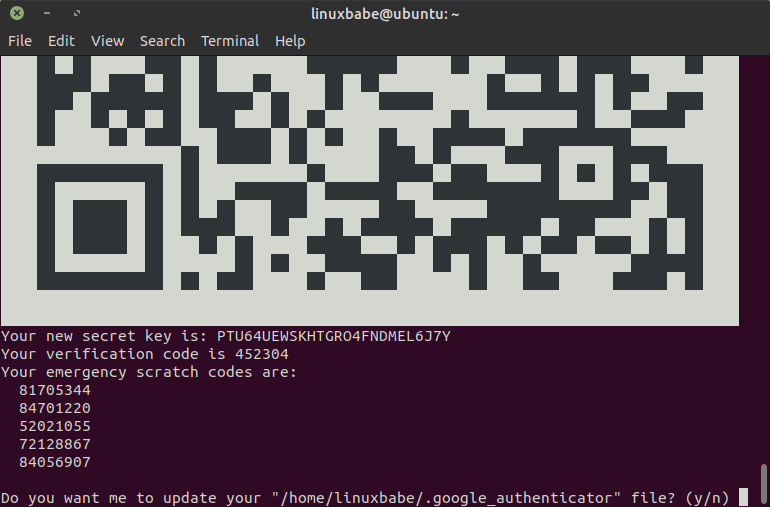
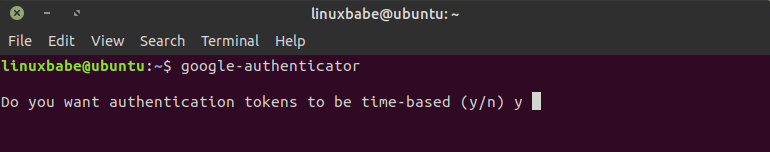
Then run the google-authenticator command to create a new secret key in your home directory.
google-authenticator
When asked “Do you want authentication tokens to be time-based?” Answer y.
#ubuntu #2fa #linux desktop #security #ssh