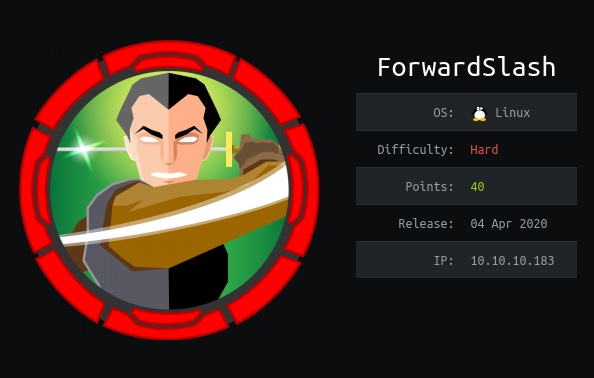
ForwardSlash is a Hard difficulty machine from Hack the Box created by InfoSecJack & chivato. My process involved Local File Inclusion (LFI), custom binary exploit, and cryptography.
_This is a raw walkthrough, so the process of me falling through rabbitholes upon rabbitholes are well documented here. It also reflects my thought process __while _I was going through the machine and I hope this can help shape how other aspiring penetration testers like me think better moving forward.
Summary:
This machine starts with a hacked webpage that’s non-interactive. We need to enumerate our way to find a backup wepage that we later discover as actually susceptible to LFI attacks, which, when successfully exploited, leaks hard-coded credentials in one of the php files contained within the server. Upon getting an initial shell, we need to exploit a custom backup program to be able to traverse laterally to the other user. This user has specific sudo privileges that we can then exploit to become root, but not until after we are able to extract the key from a cipher that used a custom encryption algorithm.
Throughout this walkthrough, I’ll be leaving superscripts as points for discussion at the very end.
Before I usually get started, I add the machine’s IP into my /etc/hosts file for easier access.
$ sudo vi /etc/hosts
~ 10.10.10.183 forwardslash.htb
Initial Reconnaissance
$ nmap -p- --min-rate 1000 -T4 forwardslash.htb
$ nmap -sC -sV -T4 -p 22,80 forwardslash.htb -oN nmap.txt
I use the first nmap command to make sure that I’m able to cover all ports of the machine I’m testing. Once the first command returns its initial results, I then plug the available ports in the second nmap command for a more detailed look.

Detailed nmap results
It’s quite straightforward, as the usual ports 22, and 80 are open in this machine.

Looks like they’re hacked haha
This is what greeted me as I checked the home page. It’s a defaced website that is absolutely non-interactive. The first time I checked this, I actually backed out and solved another machine because I was deeply intimidated then. lol.
When I got back into solving this one, since there’s nothing else I can do, I started dirbusting the site to check for breadcrumbs that I can work with.

I screencapped this as soon as it appeared as it seemed interesting, and upon checking the resource, it gave the following clue:

Which essentially translates to “bro, issaprank, you need to enumerate more”
VHOST, and Backup Website
Upon checking through more stuff, I found nothing. I then remembered, I haven’t tried domain enumeration.¹ Upon going back to the clue above, I tried editting my /etc/hosts file by adding the entry backup.forwardslash.htb
$ sudo vi /etc/hosts
~ 10.10.10.183 forwardslash.htb backup.forwardslash.htb
Upon hitting the domain, this page greeted me:

Alrighttt
I tried a few common SQLI payloads but I didn’t get anywhere. I then tried usual usernames and passwords and something interesting came up.
#linux #hacking #local-file-inclusion #hackthebox #pentesting